What the pitch says about the technology
You are the CEO, CFO, or CHRO of a medium to large size organization and receive this pitch to deploy some new technology from your CIO or Director of IT: 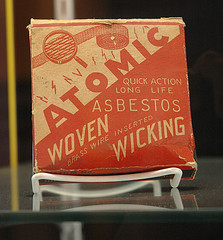 Flickr- Marshall Astor
Flickr- Marshall Astor
We’re going to deploy some expensive technology that makes it extremely cumbersome for anyone to share information throughout the company. We anticipate that people will use it to enter transactions, run reports, process workflows, and complain to their colleagues about the new system, how they were not trained adequately, and how they long for the old system.
We’ll recruit an initial set of users, drawn from both high and low places in the company, and including very few formal and informal leaders.
We will create and issue detailed guidelines and policy statements, we’re not going to trust our employees and it will be easy to make mistakes, but hard to correct them. We’ll monitor usage, and if anyone misuses the technology we’ll eventually figure it out, and take corrective action.
We’re going to run this pilot for a year or more, at the end of which we’ll report back to you with lessons learned and benefits received.
Crazy right? Would you as the decision maker buy-in to this project? Wouldn't you be wondering just who in their right mind would bring you such hopeless pitch?
Expensive, highly inflexible, will take forever to deploy, and most of the users will hate it? Sounds like the kind of project that will get you fired.
How about if the pitch was changed just a bit - and you heard this coming from the mouth of the CIO?
We’re going to deploy some cheap technology that makes it extremely easy for anyone to share information throughout the company. We anticipate that people will use it to post insights, point to good content, ask questions, and tell their colleagues what they’re working on, what they’re seeing, and what they’re learning.
We’ll recruit an initial set of regular contributors, drawn from both high and low places in the company, and including both formal and informal leaders.
Rather than coming up with and issuing detailed guidelines and policy statements, we’re instead going to trust our employees and make it easy to correct mistakes instead of hard to make them. We’ll monitor contributions, and if anyone misuses the technology we’ll learn about it quickly and take corrective action.
We’re going to run this pilot for x months, at the end of which we’ll report back to you with lessons learned and benefits received.
Last week on Andrew McAfee's blog, McAfee offered the preceding as a low-key 'Enterprise 2.0' technology sales pitch. The pitch at the very start of this post is my (hopefully) creative modification of McAfee's pitch for a traditional, big enterprise technology.
The key to the Enterprise 2.0 pitch, and to the underlying types of technology that are being pitched is simplicity, flexibility, and usefulness to BOTH the individual and to the organization.
Big, classic enterprise software projects like ERP or Supply Chain Management are by definition expensive, time consuming, and incredibly inflexible. Drop $5M on a large ERP suite and you are living with it for a long time. Heck, in big organizations just keeping the restrooms stocked with TP is a big, complicated undertaking.
But the difference in the tone of the two fake pitches is, I think, telling. People and organizations are desperate for more technologies that the Enterprise 2.0 pitch promises, while continually being drawn back into the familiar and painful clutches of Enterprise 1.0.

 Steve
Steve

Reader Comments (4)
I happen to sell software for a living, and I love the post! I just saw some great research yesterday (that I have no affilliation with) that identifies the key driviers to software deployments being successful or not. Turns out a huge key is user adoption, which enterprise 2.0 is very good at addressing. Here's the link to the research. http://internet.ziffdavisenterprise.com/CIOI_Downloads/CIOI_200911_Research.pdf
Great post. I'll be doing my own post off of this thought line soon. In the meantime, this is something we encounter as well. It seems some decision makers allow themselves to be sucked back into the web of "the way it's always been done" -- even if that way is more expensive, less efficient, and requires a MUCH longer implementation cycle. As best I can ascertain, they do this because they are afraid of the less known and choose what they believe to be the "safe" solution, but in the process saddling their companies and their employees with a wasteful system.
@Max - Thanks very much, from a sales pro your comments are most appreciated. Thanks for sharing the link.
@Derek - Thanks! I look forward to reading your take on this. I think you are right about fear being a big factor in the desire to make the 'safe' decision.
Their protection policy also embodies the culture of replica handbags . There has ever been a survey about who are those people, who are extremely fascinated with Louis Vuitton handbag . And the result indicates that it is young white collars that are more favorable with consuming luxury goods, such as Louis Vuitton bag , wallets and pursers and so on.